An international law enforcement operation involving 11 countries has resulted in the takedown of FluBot, of one of the fastest-spreading Android mobile malware.
With cases spreading across Europe and Australia, international police cooperation was central in taking down the FluBot criminal infrastructure.
This Android malware has been spreading aggressively through SMS, stealing passwords, online banking details and other sensitive information from infected smartphones across the world. Its infrastructure was successfully disrupted earlier in May by the Dutch Police (Politie), rendering this strain of malware inactive.
FluBot was first spotted in December 2020, gained traction in 2021 and compromised a huge number of devices worldwide, including significant incidents in Spain and Finland.
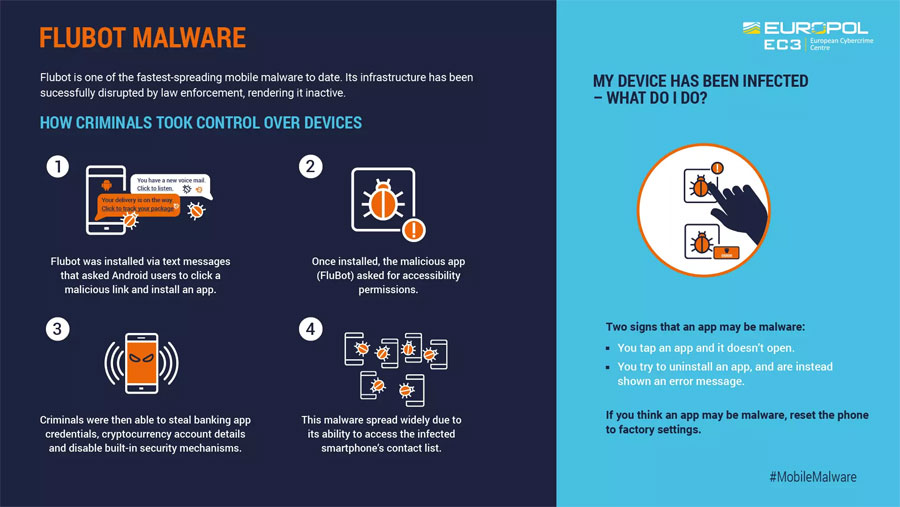
The malware was installed via text messages which asked Android users to click a link and install an application to track to a package delivery or listen to a fake voice mail message. Once installed, the malicious application, which actually was FluBot, would ask for accessibility permissions. The hackers would then use this access to steal banking app credentials or cryptocurrency account details and disable built-in security mechanisms.
This strain of malware was able to spread like wildfire due to its ability to access an infected smartphone’s contacts. Messages containing links to the FluBot malware were then sent to these numbers, helping spread the malware ever further.
This FluBot infrastructure is now under the control of law enforcement, putting a stop to the destructive spiral.
Source: